As more and more businesses are moving to the cloud, it’s paramount that security is top of mind. Protecting your users as well as your most important, sensitive and confidential data is critical to business success. If you’re considering moving to the cloud with Microsoft Office 365, here is a list of security and compliance features found in each of the Enterprise licenses (E1, E3, and E5):
Office 365 E1 Plan Security Features:
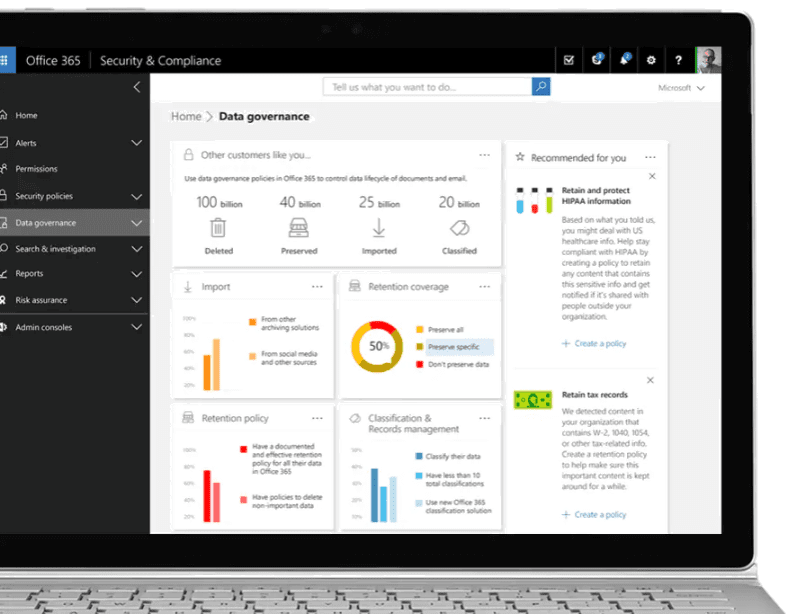
Access to the Security and Compliance Center
The Office 365 Security and Compliance Center will be your main portal for protecting your data in O365. As a global administrator, you’ll be able to manage your security and compliance settings for all of your data across O365.
Threat Management
Threat management includes capabilities like mail filtering and anti-malware. Threat managements is designed to control and manage mobile device access to your data, protect your data from data loss (intentional or not), and protect inbound and outbound messages from malicious software and spam. By leveraging Threat Management, you can determine whether senders are maliciously spoofing accounts from your domain. Microsoft continues to add new features to Threat Management, but here are some currently available additional features within the Threat Management tool:
| Mail filtering |
|
| Anti-malware |
|
| DKIM |
|
The original, expanded version of this table is available here.
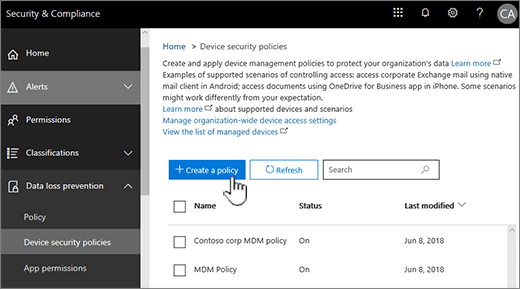
Mobile Device Management
Mobile Device Management (MDM) helps you secure and manage your users’ mobile devices such as iPhones and iPads, Android devices, or Windows phones. You can create and manage device security policies, wipe a device remotely and view detailed device reports.
Data Governance
With Data Governance you can manage the full lifecycle of your data and content from importing and storing data to creating policies that retain and permanently delete content after a specified amount of time. Data governance enables users to create, publish, and manually apply labels to documents; import data using drive shipping or over the network; and create and apply retention/deletion policies across workloads, users, and groups. Retention policies applied to mailboxes require Office 365 Enterprise E3 (with add-on) or E5.
Search and Investigate
Search for in-place files like emails, documents, or IM conversations in your organization.
eDiscovery Search
eDiscovery search grants you the ability to search for content in Exchange Online, O365 Groups, Teams, SharePoint Online, OneDrive for Business and Skype for Business conversations.
Archiving, Manual Retention/Deletion Policies
Control when items are archived and then they will be automatically deleted to control the retention and deletion of items.
Office 365 E3 Plan Security Features:
Office 365 E3 Licenses include all of the security features included with E1 licenses.
Data Loss Prevention (DLP)
With a data loss prevention (DLP) policy in the Office 365 Security & Compliance Center, you can identify, monitor, and automatically protect sensitive information across Office 365. Sensitive information includes, and is not limited to, financial data or personally identifiable information (PII) such as credit card numbers, or social security numbers.
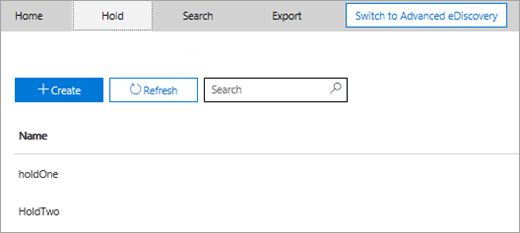
eDiscovery Export and eDiscovery Holds
Export your eDiscovery data and place holds on content or file locations to record and preserve relevant content.
Office 365 E5 Plan Security Features:
Office 365 E5 Licenses include all of the security features included with E1 and E3 licenses.
Office 365 Cloud App Security
Office 365 Cloud App Security gives you the insight into suspicious activity in Office 365 so you can investigate situations that are potentially problematic and, if needed, take action to address security issues.
Office 365 Advanced Threat Protection
Office 365 Advanced Threat Protection includes additional, advanced threat management capabilities like
| Safe Attachments | When enabled, email attachments are opened in a special, isolated environment that is separate from Office 365 before they are sent to recipient inboxes. Safe Attachments is designed to help detect malicious attachments even before anti-virus signatures are available. |
| Safe Links | Safe Links help prevent users from following URLs in email or in Office documents that point to web sites that are recognized as malicious. |
| Quarantine | Set up Quarantine for incoming email messages in Office 365 where messages that have been filtered as spam, bulk, phishing, and malware mail can be kept for later review. Both users and admins can work with quarantined messages. Users can work with just their own filtered messages in quarantine. Admins can search for and manage quarantined messages for all users. |
| Advanced threats | View the Threat Protection Status report to see information about the malicious content found and blocked by Exchange Online Protection and Advanced Threat Protection. |
Office 365 Enterprise E5 includes the full suite of capabilities included with Office 365 ATP Plan 2.
Advanced Data Governance
Use Advanced Data Governance to take advantage of mailbox retention policies.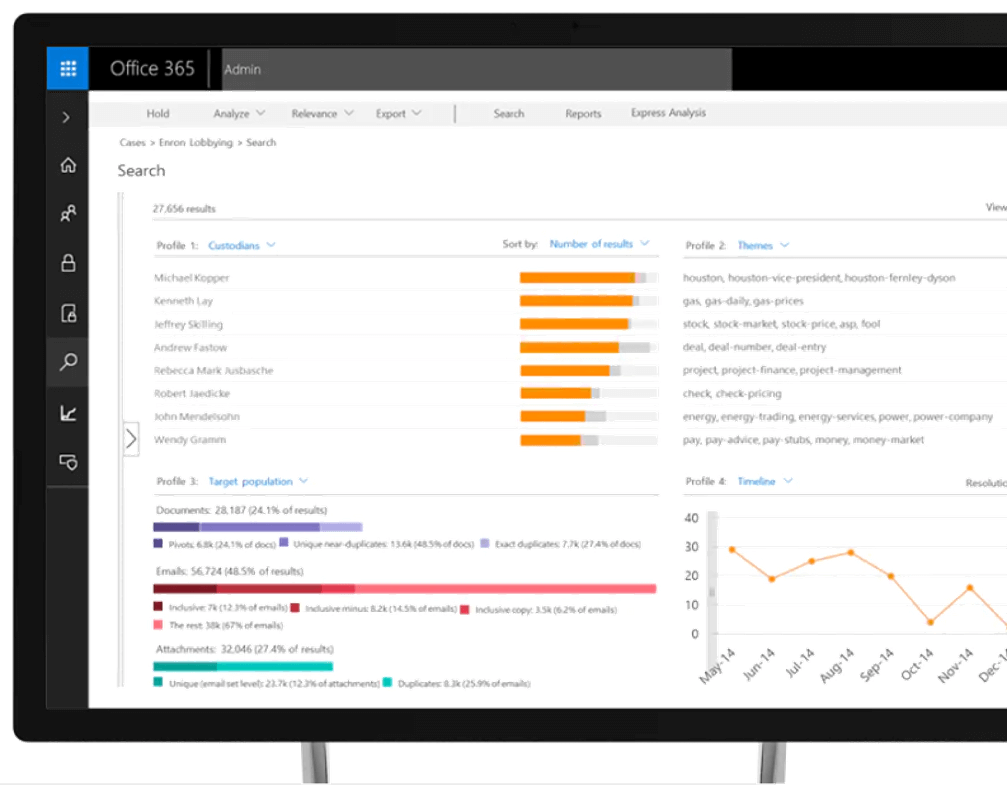
Advanced eDiscovery
Advanced eDiscovery includes eDiscovery results analysis to analyze unstructured data in your Office 365 environment through text analytics, machine learning, and relevance/predictive coding capabilities. Learn more here.
Keep Your Environment Secure with Office 365
As malicious attacks continue to advance in sophistication, Office 365’s robust set of security and compliance features can help you stay ahead. If’ you’re interested in moving your data to Office 365, contact us to help you decide which plan best meets your security needs. Already have Office 365? We can run an assessment of your Office 365 environment to make sure your data is protected!
Matt Dixon, PEI